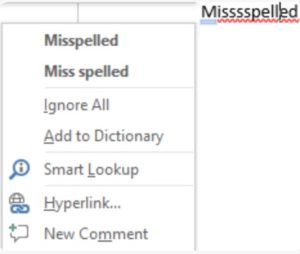
These days, most of us use our cell phones for a lot of e-mail and texting. When we need to write a more serious document, we will look to a Microsoft, Apple, or Google product to help. When we type with our smart mobile devices, while autocorrect can be annoying and shocking, it’s still very fast – and often accurate (except for those times when it is so bad it makes some blush). But when we type in a document writing tool like Google Docs or Microsoft Word, not only does it present us with the “red squiggly line” as Tom Gibbons (former Corporate Vice President for hardware, games, and mobile at Microsoft), when you do spell check to rid your document of the red squiggly line, the first suggestion is often wrong, resulting in even more clicks.
We have all come to accept this.
But how did we get here? It’s one of those things that just sounds crazy when you say it.
At what point did it become OK for our smart mobile devices, about one 20th the size of our laptops, to be better at basic tools for helping us write things?
When did that fork in the road happen, and why didn’t we raise our hands and say “excuse me . . . but isn’t backwards?”
The fact is that all of the major word processing tools we use lag behind the most familiar smart phone technology. The good news is that there is a simple solution. Yesterday morning I had coffee with Tom Gibbons and ActiveWords co-founder Buzz Bruggeman, both Seattleites to discuss this.
ActiveWords does many things – but at the end of the day, it’s greatest value is in saving keystrokes for the words, phrases, even the paragraphs you type most.
Buzz was asking Tom – whom to speak with at Microsoft about how to get ActiveWords embedded in all keyboards, given success ActiveWords has had with their customers – not the least of which is a 92% renewal rate for their product. Tom said that he’d think of it differently, for a variety of reasons. He said instead of talking with hardware people (who have an unusual relationship with the operating system team), he suggested that Buzz should present ActiveWords to Microsoft Office, as the bridge to this laptop/smartphone gap – it’s so clear and felt by all of us – Apple, Google, and Microsoft would be crazy not to take that meeting because the problem statement is so clear. ActiveWords has already solved the problem, they have a very solid installed base in Microsoft Windows with a beta for Apple’s iOS.
Big companies like to make bets that will turn into multi-billion dollar revenue streams. Amazon’s Jeff Bezos says many of those ideas should be thought of like acorns that start out as small things that become giant trees – where patience sometimes takes years. This is no acorn. This is about protecting the already multibillion dollar revenue streams of Microsoft Office, Google Docs, and Apple’s platform.
Sounds like an ovious solution to me.